Cyber Security Solutions
- Home
- Cyber Security Solutions
Consolidate your cybersecurity with Sophos
Sophos Firewall is much more than a firewall — it’s the heart of the world’s best network security platform. Consolidate and simplify your cybersecurity with a single vendor, cloud management console, and agent.

Consolidate your cybersecurity with Sophos
- Full next-gen firewall optimized for the modern encrypted internet, offering industry-leading protection and performance
- Integration with Sophos MDR and Sophos XDR for automated threat response and synchronized security to stop threats before they cause a serious problem
- Comprehensive SD-WAN capabilities that let you easily and securely orchestrate and interconnect your various offices and locations
- Integration with our cloud-delivered network security solutions, including Sophos Zero-Trust Network Access (ZTNA), DNS Protection, Zero-Day Threat Protection, and more
- Built-in ZTNA for secure and easy remote worker access
- Cloud management and reporting from Sophos Central for managing operations across all your firewalls, wireless networks, switches, ZTNA, endpoints, mobile devices, servers, email protection, and more
Unrivaled performance
The XGS Series of next-gen firewall appliances delivers Sophos Xstream-accelerated performance at every price point to power the protection you need for today’s diverse, distributed, and encrypted networks.

Powered by Xstream
The Sophos Xstream architecture accelerates and offloads your important SaaS, SD-WAN, VPN, and cloud traffic at the hardware or software level from our deep packet inspection (DPI) engine. On some models, it performs Transport Layer Security (TLS) and DPI using integrated Sophos Xstream Flow processors.
Performance by design
From the smallest entry-level device to our enterprise and campus edge models, every Sophos Firewall is custom-built to handle the most demanding workloads. Striking the perfect balance between performance, value, and efficiency, our hardware appliances unlock the high-speed connectivity you need to prevent bottlenecks and reap the full potential of your network.
High-speed connectivity
Customize your firewall’s already versatile networking options with an extensive range of add-on modules for high-speed copper, fiber, Power over Ethernet (PoE), 5G, and Wi-Fi connectivity.
FortiGate NGFWs protect any edge at any scale with industry-leading security
Next-Generation Firewall (NGFW)
FortiGate is the most deployed network firewall with over 50% of global market share. FortiGate Next-Generation Firewalls (NGFWs) protect data, assets, and users across today’s hybrid environments. Built on patented Fortinet security processors, FortiGate NGFWs accelerate security and networking performance to effectively secure the growing volume of data-rich traffic and cloud-based applications. FortiGate NGFWs, backed by FortiGuard AI-Powered Security Services, help you prevent cyberattacks and mitigate security risks with consistent, real-time protection and responses against even the newest and most sophisticated threats.

Entry-Level (Branch)

Mid-Range (Campus)

High-End (Data Center)
The Fortinet Security Fabric Extends Capabilities

SECURE SD-WAN
Deploy secure WAN infrastructure to enhance user experience, simplify operations, and lower TCO

SECURE SD-BRANCH
Optimize secure connectivity and operational agility across branches via centralized control

ZERO-TRUST NETWORK ACCESS
Ensure secure access to applications hosted anywhere, regardless where users are located

AI-POWERED SECURITY SERVICES
Stop known, unknown, zero-day, and emerging AI-based threats with comprehensive threat protection
A simple firewall with big threat-blocking benefits
Protect your small or medium business like a big business, without a big business price.
Cisco Firepower
Robust protection for small and midsize businesses
A world-class firewall solution that is easy to manage, detects more threats, but costs less.

Detect, Investigate, and Eliminate Threats at the Endpoint
Our EDR solutions provide advanced threat detection, real-time monitoring, and automated response to secure endpoints across your network. With tools like Cisco Secure Endpoint, FortiEDR, and Sophos EDR, we help businesses in Saudi Arabia protect critical data and prevent breaches before they happen — backed by expert implementation and support.

Sophos Endpoint Detection and Response (EDR)
Extend your endpoint protection with AI-powered threat detection and response.

Elevate Your Endpoint Defenses
Sophos gives you the tools to detect and respond to suspicious activity on your endpoints and servers before adversaries can impact your systems.
Elevate Your Endpoint Defenses

EDR that starts with the strongest endpoint protection built-in

Instant visibility of suspicious activity across your endpoints and servers

Prioritized detections make it easy to focus on what’s important

Rapidly contain threats with accelerated and automated response capabilities

Instant visibility of suspicious activity across your endpoints and servers

Prioritized detections make it easy to focus on what’s important
Cisco Secure Endpoint
Endpoint security built for resilience
Speed matters when it comes to endpoint security. Detect, respond, and recover from attacks with our cloud-native solution, and reduce remediation times by as much as 85 percent.
Stop threats before they compromise your business
The sooner threats are detected, the faster businesses can recover. Secure Endpoint offers advanced endpoint protection across control points, enabling your business to stay resilient.

Secure Endpoint Licencing
Secure Endpoint Essentials
Powered by Cisco Talos, we block more threats than any other security provider. See a threat once and block it everywhere. Automate threat responses with one-click isolation of an infected host.
Secure Endpoint Advantage
Take advantage of the ability to simplify security investigations with advanced endpoint detection and response to easily access your advanced malware analysis and threat intelligence portal.
Secure Endpoint Premier
With Talos Threat Hunting, elite security experts from Cisco proactively search for threats in your environment and provide high-fidelity alerts with remediation recommendations.
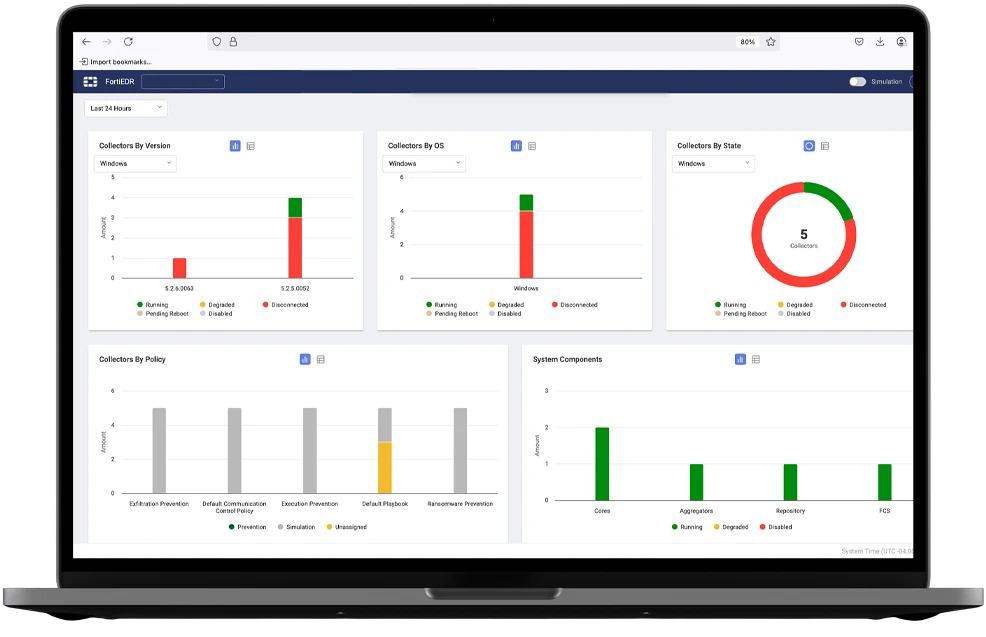
FortiEDR Advanced Endpoint Protection
FortiEDR safeguards your digital landscape with evasion-resistant, real-time protection, automated incident response, and comprehensive security capabilities tailored to enhance your cybersecurity posture for workstations, servers, and cloud workloads. Reduce the attack surface and leverage out-of-the-box policies that are tightly mapped to the MITRE ATT&CK framework so security teams can respond to a multitude of advanced tactics, techniques, and procedures found in attacks such as ransomware.
Features and Benefits

DISCOVER AND CONTROL
Discover and control rogue devices and applications based on risk mitigation policies.

DETECT AND DEFUSE IN REAL TIME
Automatically detect and defuse potential threats in real time—even on compromised devices.

AUTOMATIC INCIDENT RESPONSE
Use customizable contextual incident response playbooks that automate incident response.

DRIVE IDENTITY-BASED RESPONSE
Integrate identity tools to enhance threat detection, response, and investigation capabilities.

GAIN EFFICIENT SECURITY OPERATIONS
Eliminate alert fatigue and optimize operations with customizable incident response processes.

ENABLE FULL FEATURE PARITY
Support legacy systems like XP or Server 2003 and get full feature parity.
Digital Certificate & PKI Solutions for Secure Communication
We offer end-to-end certificate management services, including SSL/TLS certificates, email encryption, code signing, and device authentication. With trusted PKI solutions from leading providers, we help organizations in Saudi Arabia ensure data integrity, secure identity verification, and compliance across networks, servers, and endpoints.
The DigiCert® ONE Platform
Reduce outages, automate manual processes and close security gaps for all things PKI and DNS.

Certificate Lifecycle
Get full visibility across your PKI landscape and avoid outages.
Software Trust
Release secure software while lowering remediation and compliance costs.
Device Trust
Protect IoT devices with complete lifecycle security, from manufacturing to decommissioning.
Document Trust
Safeguard digital documents and transactions with trusted integrations and global compliance.
Our SSO Solutions with DUO
Identity is in crisis. Duo is the cure.
Duo flips the script on identity with security-first IAM that attackers hate and users love.
Identity security solutions for everyone
Duo’s identity security is customizable, easy to set up, and simple to use, making it the ideal solution for businesses large and small across every industry.


Any size, any team
At Duo, we believe there’s no one-size-fits-all approach to identity security. Your organization has unique security needs, and we’re here to help you meet them. Maybe you need to meet industry-specific compliance standards or protect highly sensitive customer data. Perhaps you’re looking for a solution to a particular security concern — like phishing attacks or BYOD. We can even help you future-proof your security strategy with industry-leading zero trust for the workforce. Whatever your access ask, Duo has you covered.
A complete suite of security solutions
Whether you’re considering a big-picture security strategy like zero trust, or you want to address a specific threat like phishing attacks, Duo has you covered.

Continuous Identity Security
Move toward a passwordless future. Stop sophisticated identity attacks and ensure a seamless authentication experience for every member of your team.

Access management
Access management is a set of tools and policy controls that make sure only the right users have access to the right applications and resources, under the right conditions.

Zero trust security
Duo’s zero trust capabilities help you bring more security to the ever-changing, no-boundaries, work-from-anywhere world.

Passwordless authentication
We’ve set the stage for user-friendly, password-free multi-factor authentication with Duo’s comprehensive access security.\

Phishing prevention
Secure your workforce against phishing attacks with strong multi-factor authentication, device trust and more.

Risk-based authentication
Duo’s dynamic risk-based authentication solution detects and responds to potential threat signals to secure trusted users and frustrate attackers.
Advanced Email Security Solutions
Safeguard your organization from phishing, malware, and business email compromise (BEC) with our robust email security offerings. We provide deployment and support for industry-leading platforms that include threat intelligence, email encryption, spam filtering, and advanced malware detection. Whether on-premises or cloud-based, our solutions ensure compliance and uninterrupted communication—protecting both inbound and outbound messages.
Stop Phishing.
Protect Email Data.
Trust your inbox with Sophos Email security.

Prevent Phishing and Imposter Threats
Trust your inbox again with cloud email security protecting your people and critical information from malware, as well as malware free phishing and impersonation attempts.
Keep Imposters Out
Automatically identify your high-profile targets for malware-free impersonation and business email compromise attacks, then block the attack with machine learning analysis of message content.
Let Trusted Senders In
Authenticate all your senders without blocking legitimate email using SPF, DKIM, and DMARC authentication techniques and email header anomaly analysis.
Stop Malware From Reaching the Inbox
Multi-layered protection utilizes over 35 years of threat intelligence, reputational and behavioral analysis, and state-of-the-art machine learning to eliminate malware and malicious URLs from reaching your inboxes.
Protection Post-delivery
Automatically remove phishing emails containing newly infected URLs as soon as the threat state changes with continuous monitoring of Microsoft 365 mailboxes.
Our Network Partners







